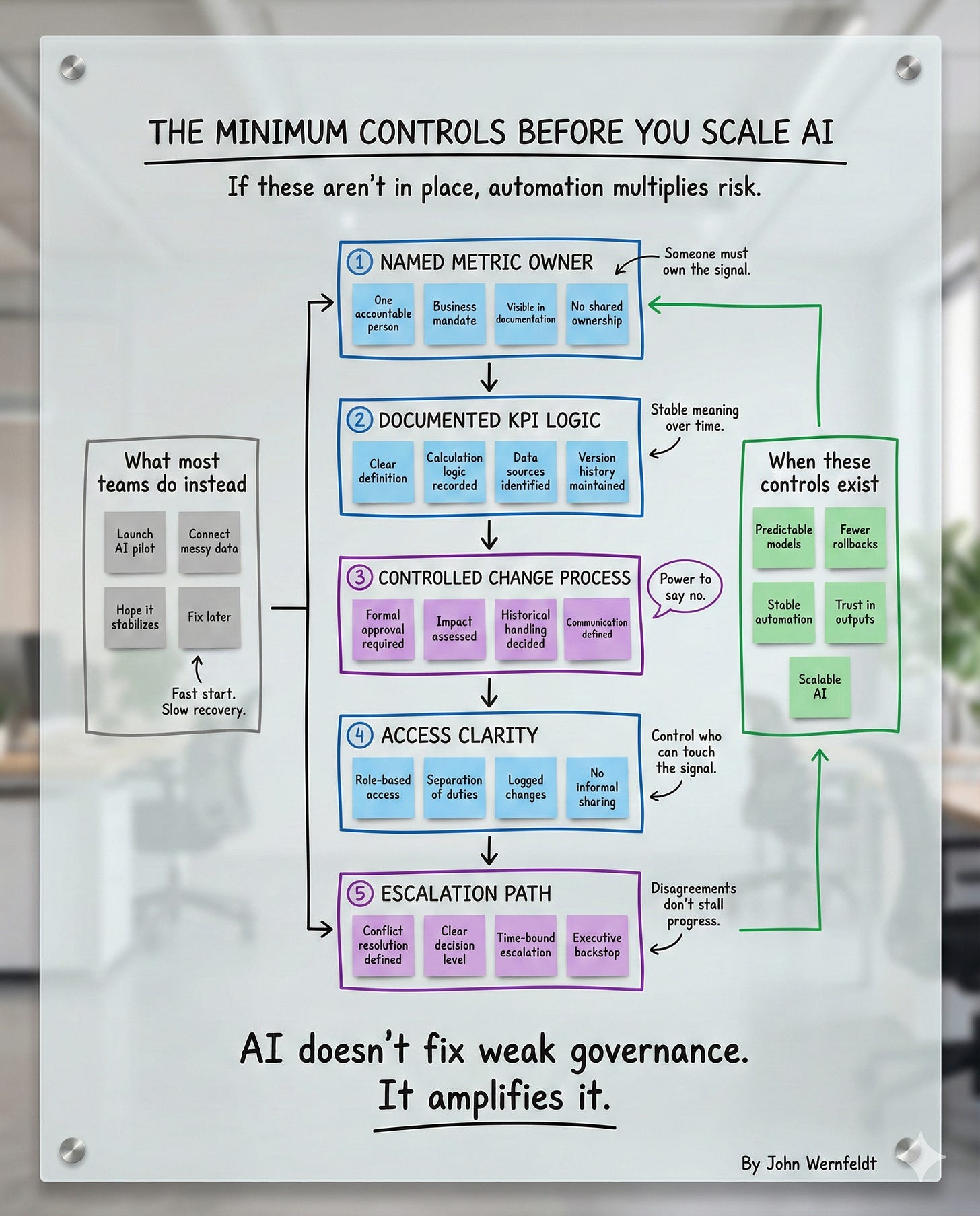
The Minimum Controls Before You Scale AI
If these aren’t in place, automation multiplies risk.
Everyone wants to scale AI.
Nobody wants to talk about what happens when you scale AI on top of broken governance.
I’ve seen it happen dozens of times.
A company launches an AI pilot. It works. Leadership gets excited. The mandate comes down: scale this across the organization.
Six months later, the model is rolled back. Or worse, it’s still running but nobody trusts it.
The problem is never the model.
The problem is that AI doesn’t fix weak governance.
It amplifies it.
And when you scale automation on top of ambiguity, you don’t get efficiency.
You get predictable chaos at speed.
Here’s what most teams do instead of building the foundation:
Launch an AI pilot
Connect messy data
Hope it stabilizes
Fix later
Fast start. Slow recovery.
Here’s what actually works:
Build the minimum controls before you scale.
Not a full governance overhaul. Not a two-year data quality program.
The minimum layer that makes automation safe to sustain.
Five controls. Non-negotiable.
Let me walk you through them.
Control 1: Named Metric Owner
Someone must own the signal.
Not a committee. Not a working group. Not “the data team.”
One accountable person.
Every metric that feeds your AI model needs a named owner who is responsible for:
Business mandate — What does this metric actually measure and why does it matter?
Visible in documentation — Anyone can look up who owns what
No shared ownership — Shared ownership is no ownership
Why this matters
AI models consume metrics. If nobody owns the metric, nobody is accountable when the signal changes unexpectedly.
And the signal always changes.
Markets shift. Business logic evolves. Data sources get updated.
When that happens, someone needs to decide: is this change valid or is this a problem?
If the answer is “we’ll discuss it in the next governance meeting,” you’re already too late.
The model has been running on bad data for weeks.
What breaks without it
I watched a retail client roll back a demand forecasting model because “active customer” was defined differently across three regions.
The model trained on one definition. Production used another. The forecast was off by 20%.
Nobody caught it because nobody owned the metric.
When the rollback happened, leadership asked: “Who approved this definition?”
The answer: “We thought marketing owned it.”
Marketing’s answer: “We thought finance owned it.”
Finance’s answer: “We thought it was a data engineering question.”
Three months of work. Rolled back in one meeting.
Named ownership prevents that.
Control 2: Documented KPI Logic
Stable meaning over time.
Once you have a named owner, the next control is documentation.
Not buried in someone’s head. Not scattered across Confluence pages.
Centralized. Versioned. Accessible.
Here’s what documented KPI logic includes:
Clear definition — Plain language explanation of what the metric measures
Calculation logic recorded — The exact formula, including edge cases
Data sources identified — Where the data comes from and how it’s transformed
Version history maintained — Every change is logged with a reason and a date
Why this matters
AI models need stable inputs.
If the definition of “revenue” changes halfway through the training period, the model learns the wrong pattern.
If the calculation logic changes in production without updating the model, predictions become unreliable.
Documentation creates stability.
Not bureaucracy. Stability.
What breaks without it
A financial services client deployed a credit risk model that flagged 30% more customers as high-risk than expected.
The reason: the definition of “missed payment” had changed three months earlier.
The data engineering team updated the logic in the source system. The documentation wasn’t updated. The model team didn’t know.
The model was still using the old definition in its training data but the new definition in production.
Result: false positives, customer complaints, and a model that lost trust.
Documentation prevents that.
Control 3: Controlled Change Process
Power to say no.
This is where most organizations fail.
They document the metric. They assign an owner.
Then someone makes a change without approval and everything breaks.
A controlled change process means:
Formal approval required — No one changes core logic without sign-off
Impact assessed — Before approval, someone evaluates what breaks downstream
Historical handling decided — Do we restate history or treat this as a new metric?
Communication defined — Who needs to know and how do they get notified?
Why this matters
AI models are downstream dependencies.
When you change a metric definition, you’re changing the input to a system that was trained on the old definition.
That’s not a small thing.
Most organizations treat metric changes like configuration updates. Quick. Low-risk. Easy to reverse.
They’re not.
Metric changes are schema changes to your business logic.
They need to be treated that way.
What breaks without it
A logistics company updated their “on-time delivery” calculation to exclude weekends.
Reasonable change. Better aligns with how customers experience the service.
The change was made in the reporting layer. The AI model predicting delivery times wasn’t updated.
For two months, the model was training on a definition that no longer matched production.
By the time they caught it, the model had drifted so far that retraining from scratch was faster than fixing it.
Six weeks of work. Lost.
Change control prevents that.
Control 4: Access Clarity
Control who can touch the signal.
Once you have ownership, documentation, and change control, the next layer is access.
Who can read the data?
Who can write to it?
Who can change it?
If the answer is “anyone with database access,” you don’t have control.
Here’s what access clarity looks like:
Role-based access — Permissions tied to job function, not individual requests
Separation of duties — Read access ≠ write access ≠ change approval
Logged changes — Every modification is traced to a person and a timestamp
No informal sharing — Data doesn’t move via Slack, email, or shared drives
Why this matters
AI models are only as trustworthy as the data that feeds them.
If anyone can modify the source data without a trace, you can’t trust the model output.
And if you can’t trust the output, you can’t scale the model.
Access control isn’t about gatekeeping.
It’s about traceability.
When something goes wrong, you need to know who changed what and when.
What breaks without it
A healthcare client had an AI model flagging patient risk based on medical history data.
One day, the model started flagging 40% more patients as high-risk.
Investigation revealed that a data analyst had manually corrected a batch of records to “fix a data quality issue.”
The correction was well-intentioned. But it wasn’t logged. And it wasn’t approved.
The model retrained on the corrected data and learned a new pattern.
By the time they figured it out, the model had been running for three weeks.
Thousands of patients flagged incorrectly. Clinical workflows disrupted.
Access clarity prevents that.
Control 5: Escalation Path
Disagreements don’t stall progress.
This is the most overlooked control.
You can have named owners, documented logic, change control, and access clarity.
But if two owners disagree about a definition and there’s no one with the authority to break the tie, nothing moves.
An escalation path means:
Conflict resolution defined — When two owners disagree, who decides?
Clear decision level — Escalation doesn’t mean “more meetings.” It means a specific person at a specific level makes the call.
Time-bound escalation — Decisions happen within a defined window (24 hours, 48 hours, one week — whatever fits the context)
Executive backstop — If the first level can’t decide, there’s a second level. And a third. All pre-defined.
Why this matters
AI doesn’t wait for consensus.
If you’re running a model in production and a definition dispute stalls a fix, the model keeps running.
On bad data.
Until someone with authority makes a call.
Most organizations don’t define that authority up front.
They assume goodwill and collaboration will resolve disputes.
They won’t.
Not at scale.
What breaks without it
A manufacturing client had two metric owners arguing over the definition of “machine downtime.”
Operations wanted to exclude planned maintenance. Finance wanted to include it.
Both had valid reasons.
But nobody had the authority to decide.
The argument went on for six weeks.
Meanwhile, the AI model predicting maintenance schedules was training on inconsistent data.
By the time leadership stepped in and made the call, the model had already been deployed to three plants.
It performed poorly. Trust was lost. The rollout stalled.
Escalation paths prevent that.
When These Controls Exist
Here’s what happens when you build these five controls before scaling AI:
Predictable Models
The model behaves consistently because the inputs are stable.
Fewer Rollbacks
You catch definition drift before it reaches production.
Stable Automation
Changes are controlled, so downstream systems don’t break unexpectedly.
Trust in Outputs
Leadership trusts the model because they trust the data feeding it.
Scalable AI
You can deploy the same model to new teams, new regions, new use cases without starting over.
That’s not theory.
That’s what happens when governance scales with ambition.
What Most Teams Do Instead
Here’s the pattern I see over and over:
1. Launch AI pilot
Pick a use case. Build a model. Test it on a small dataset.
2. Connect messy data
Pull data from whatever systems are easiest to access. Don’t worry about ownership or definitions. “We’ll clean it up later.”
3. Hope it stabilizes
Deploy the model. Monitor performance. Hope the data quality doesn’t degrade.
4. Fix later
When something breaks, form a working group. Discuss the issue. Assign action items. Repeat.
Fast start. Slow recovery.
And the recovery is always more expensive than building the controls up front would have been.
The Real Cost of Skipping the Foundation
Let me make this concrete.
I worked with a client who deployed an AI-powered pricing model across 15 regions.
No named owners for the pricing metrics. No documented logic. No change control.
Three months in, regional teams started making pricing adjustments based on local market conditions.
Reasonable. Expected.
But nobody told the model team.
The model kept training on assumptions that no longer matched reality.
By the time they caught it, the model was recommending prices that were 10-15% off market in half the regions.
Lost revenue. Angry regional leaders. A six-month pause to rebuild trust.
The total cost: $2.3M in lost margin + six months of opportunity cost + credibility damage that took a year to repair.
The cost to prevent it:
2 weeks to define metric ownership
1 week to document KPI logic
1 week to set up change control
1 week to clarify access roles
1 day to define the escalation path
Five weeks of setup work to prevent a multi-million dollar failure.
That’s the trade-off.
How to Implement the Minimum Controls
If you’re about to scale AI and these controls aren’t in place, here’s how to build them:
Step 1: Identify the Critical Metrics
List every metric that feeds your AI model. Not every metric in your organization. Just the ones the model depends on.
Usually 10-20 metrics for a single model.
Step 2: Assign Named Owners
For each metric, assign one person who is accountable for its accuracy, definition, and business meaning.
Not a team. A person.
Document it in a system of record (not a spreadsheet).
Step 3: Document the Logic
For each metric, write down:
What it measures
How it’s calculated
Where the data comes from
When it was last changed and why
Version control this. Treat it like code.
Step 4: Define the Change Process
Create a simple approval workflow:
Who can request a change?
Who approves it?
What’s the impact assessment process?
How is the change communicated?
This doesn’t need to be complex. It needs to be clear.
Step 5: Clarify Access
Map out who has read, write, and change permissions for each metric.
Remove access that doesn’t need to exist.
Log all changes.
Step 6: Set the Escalation Path
Define who breaks ties when metric owners disagree.
Name the person. Set the timeline. Document it.
The Timeline Question
Here’s the question I always get:
“How long does this take?”
Answer: 4-6 weeks for a single AI use case.
Not 4-6 weeks of dedicated work.
4-6 weeks of calendar time with a part-time working group.
Most of the work is decision-making, not implementation.
Deciding who owns what. Deciding what the definitions should be. Deciding who has authority.
Once those decisions are made, the implementation is straightforward.
The ROI of Building the Foundation
Here’s what you get in return for those 4-6 weeks:
Faster scaling
When the first model works, you can replicate it to new use cases without rebuilding the foundation.
Lower failure rate
Models don’t break because definitions changed without warning.
Higher trust
Leadership trusts the output because they trust the governance layer underneath it.
Cleaner rollbacks
When you do need to roll back a model, you can do it cleanly without breaking downstream systems.
Predictable performance
Model drift is easier to detect and fix because you have stable baselines.
That’s the trade.
Six weeks of setup work for years of reliable automation.
The Pattern That Always Fails
Here’s what doesn’t work:
“We’ll pilot the AI first, then fix governance once we prove the value.”
I’ve heard that line a hundred times.
It never works.
Because once the pilot succeeds, the pressure to scale is immediate.
Leadership doesn’t want to hear “we need six weeks to build governance before we can scale.”
They want to hear “we’re deploying to 10 more teams next quarter.”
And if you say “we can’t scale safely yet,” you lose momentum.
So teams scale anyway.
On broken foundations.
And the failures start six months later.
By then, the governance work is 10x harder because you’re retrofitting controls onto live systems.
Build the foundation first.
Not after the pilot.
Before.
AI Doesn’t Fix Weak Governance. It Amplifies It.
That’s the headline.
If your metric ownership is unclear, AI will scale that ambiguity across every prediction.
If your change process is informal, AI will break every time someone makes an unapproved change.
If your access controls are loose, AI will train on corrupted data.
If your escalation paths are undefined, AI will stall every time there’s a dispute.
AI is an accelerant.
It accelerates value when the foundation is sound.
It accelerates failure when the foundation is weak.
The choice is yours.
The Five Controls (Summary)
Here’s the checklist:
1. Named Metric Owner
One accountable person per metric
Business mandate defined
Visible in documentation
No shared ownership
2. Documented KPI Logic
Clear definition in plain language
Calculation logic recorded
Data sources identified
Version history maintained
3. Controlled Change Process
Formal approval required
Impact assessed before changes
Historical handling decided
Communication defined
4. Access Clarity
Role-based access established
Separation of duties enforced
Logged changes tracked
No informal sharing
5. Escalation Path
Conflict resolution defined
Clear decision level established
Time-bound escalation process
Executive backstop identified
The Bottom Line
You can scale AI without these controls.
You just can’t sustain it.
The failures will come six months in. Maybe nine. Maybe twelve.
But they’ll come.
And when they do, you’ll spend more time retrofitting governance onto live systems than you would have spent building the foundation up front.
AI doesn’t fix weak governance. It amplifies it.
Build the minimum controls before you scale.
Not after.
What’s your experience?
Have you scaled AI on top of weak governance? What broke?
Or have you built the foundation first? What did you learn?
Let me know in the comments.
This framework is based on real enterprise AI implementations. Names and numbers have been changed, but the pattern holds across industries.


Yes John! I really wish more people were writing about how to own and scale the signal from their first forays into AI use rather than trying to retrofit it when the horse had bolted. 🙏
“AI doesn’t fix weak governance. It amplifies it.” Agreed.
I’d add: the next step is making high-stakes outputs cryptographically accountable at creation time, not just governed after the fact.